Required Permissions
| API | Permissions Name | Type | Description | Admin Consent Required |
|---|---|---|---|---|
| Microsoft Defender ATP | Machine.Read.All | Application | Read all machine profiles | Yes |
Setting Up Microsoft Defender for Endpoint Device Integration
In Tier Zero Code, go to “Integrations” and click on the Microsoft Defender for Endpoint device integration then enable and configure integration.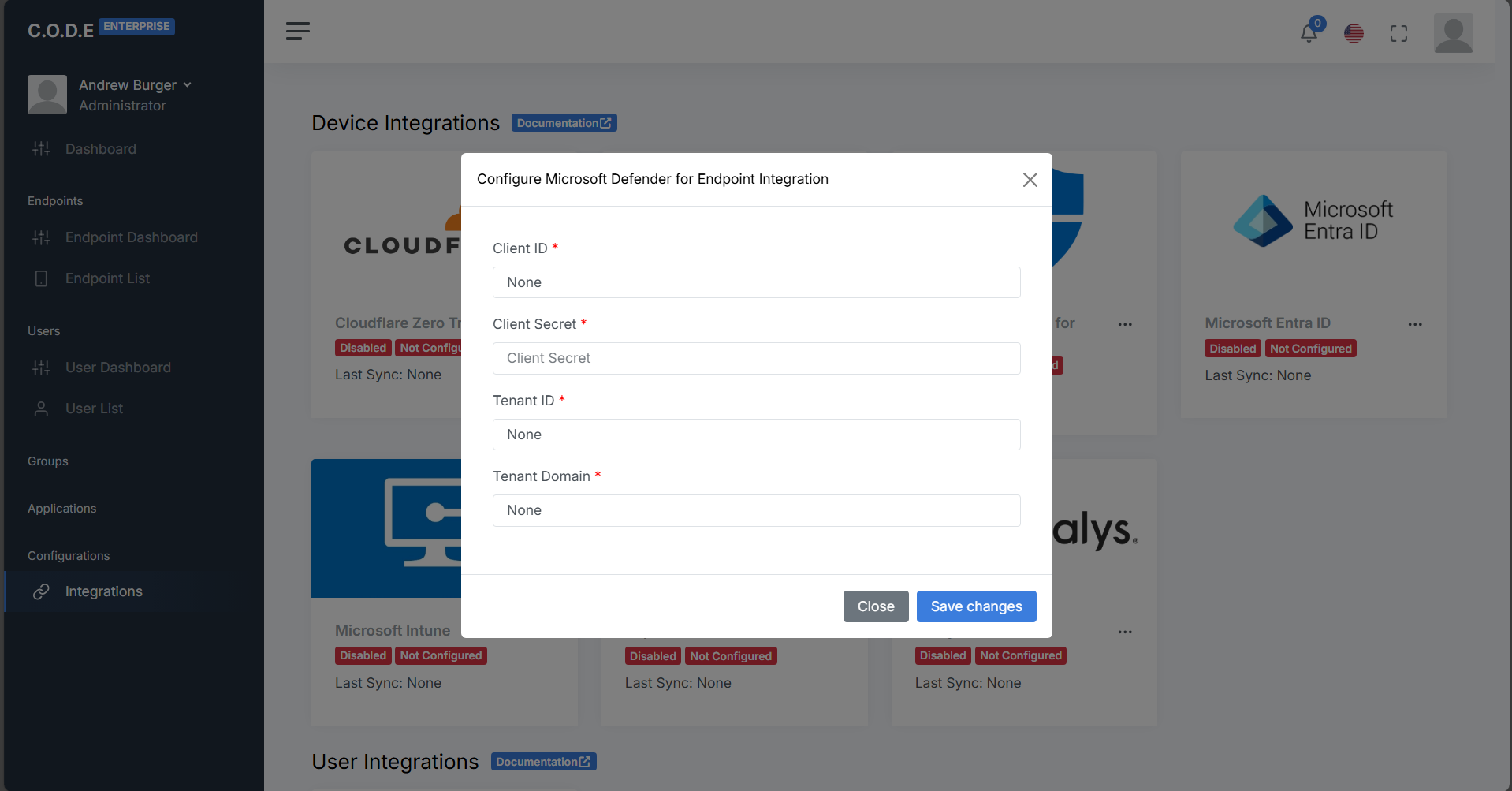
The application (client) ID from the “Overview” section of your app registration
The client secret value from the “Certificates and secrets” section of your app registration
The directory (tenant) ID from the “Overview” section of your app registration
The primary domain from the “Home” of your Microsoft Entra admin center.